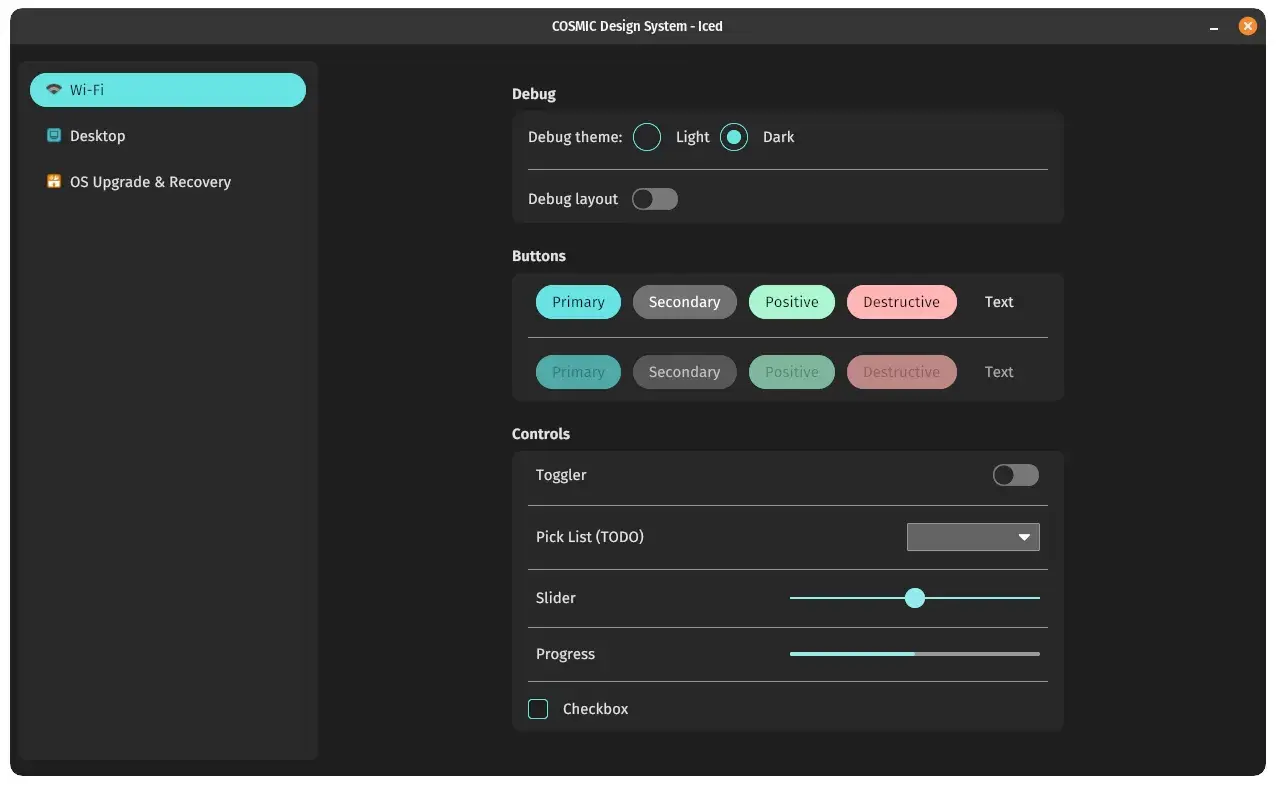
aspiring Rustacean, JavaScript jockey, 3D printing addict, use Arch Linux btw, Apple-captive, Google-captive, Meta-escapee, parent, spouse, cisgender, he/him
- 40 Posts
- 56 Comments

 9·4 months ago
9·4 months agoI’m currently using Signal, and happy with it, but they still don’t have reproducible builds, making it impossible to confirm that the code we can read on GitHub is actually what is running on my device
So, even now, it could be doing something that isn’t able to be audited
I guess Element/Matrix or Briar are the better options from this perspective, without losing any end to end encryption
Can I ignore flatpak indefinitely?
Sure, at least until software you want to use is flatpak only, e.g. Bottles

 2·5 months ago
2·5 months agoI agree that there are much bigger problems, but those bigger problems have solutions that are not allowed under capitalism and USA imperialism, so labels is all we’re allowed to fix 🤷
The legal drinking age in Australia is 18 years old, and it has always struck me as odd that it’s so high in the USA

 71·5 months ago
71·5 months agoAustralian sports fields are covered in alcohol logos So the entire time you are watching football with your children, they are exposed

 56·5 months ago
56·5 months agoBan all advertising for alcohol, too, please

 56·6 months ago
56·6 months agoI know Google just donated to Trump’s inauguration, and also does all the stupid surveillance capitalism crap that Google does, but I just compared prices, and Google Workspace is a few dollars per month cheaper per user than Proton is, for my needs (family, custom domain names, etc)
We’ve been on Proton for a few years, and it’s fine, but we do also have Pixel Android phones, and not using Google services constantly feels like swimming upstream, plus all family members also still end up having to use Google services for work, anyway
It’s just not practical for me to de-Google, which is a shame, so I think I’ll be switching in a few months, unless pricing changes significantly :S

 2·6 months ago
2·6 months agoThanks for sharing! <3

 2·6 months ago
2·6 months agoOkay, let’s go with
xtermrunningbash, where the user ranls, soxterm->bash->ls…lsnever talks toxtermdirectly, it’s stdout/stderr are provided bybashbasheffectively outputs a grid of characters toxterm,xtermdoesn’t know about prompts or words or line feeds, just the grid- every time
lsoutputs a line,bashadds a row of output to the grid that it sends toxterm - if there’s not enough space for a new row,
bashdiscards the top-most row, moves all other rows up by one row, and then inserts the row for thelsoutput
Now imagine a hypothetical fork of
bashor some other new shell …- the only thing different is the direction that the rows move off the edge of the screen when running out of space, that’s all
Thus, this is entirely a shell problem, with a shell solution
However, what I’ve neglected to mention so far is that terminal emulators and shells are almost certainly optimised for rows dropping off the top edge and new rows being added to the bottom edge
So, the role of a terminal emulator in this scenario could be to provide ANSI control characters or other protocol for operating just as quickly in the opposite direction, sure

 2·6 months ago
2·6 months agoThere’s also https://www.waveterm.dev/ which seems to be an open-source attempt at something sort of like Warp/Jupyter
I don’t mind that it uses the web stack for rendering, but that’ll probably turn some folks off

 4·6 months ago
4·6 months agoSeems like a shell feature, and not a feature that a terminal emulator would implement

 62·8 months ago
62·8 months agoThe whole thing is weird and the CEO especially so, and not weird in a good way: https://d-shoot.net/kagi.html

 1·8 months ago
1·8 months agohttps://www.partykit.io/ sort of? maybe?

 20·9 months ago
20·9 months agoGosh darn it I only just onboarded to Omnivore a few months ago Now I guess I need to find a new place to store bookmarks

 2·10 months ago
2·10 months agoOne example I can think of is Widevine DRM, which is owned by Google and is closed source: https://en.wikipedia.org/wiki/Widevine
Google currently allows Mozilla (and others) to distribute this within Firefox, allowing Netflix, Disney+, and various other video streaming services to work within Firefox without any technical work performed by the user
I don’t believe Google would ever willingly take this away from Mozilla, but it’s entirely possible that the movie and music industries pressure Google to reduce access to Widevine (the same way they pressured Netflix into adopting DRM)
For disappearing messages to work, your conversation partner has to promise they won’t take photos of their screen, and they have to promise to use an app that actually implements the feature instead of just pretending to, and the app developers have to promise to have implemented the code to delete a message when the service says it should
Is there actually a cryptographically-sound and physically-complete method for ensuring that a message is only legible for a temporary duration once it leaves your own device and is delivered to someone elses?

 10·1 year ago
10·1 year agoHmmm, is CloudFlare known for being a bad actor in terms of privacy?
Setting that aside, no matter what you pick, you’ll be exposing your IP address, from which your ISP and/or general location may be derived
If you don’t trust CloudFlare with that information then you basically cannot trust anyone else, so maybe you’d need to run your own service and ping that instead now that you’re in a situation where you can only trust yourself 🤷
The other issue that comes to mind is that you’re only testing reachability to one address, which means you could get a false negative where that address stops working but the rest of the internet is actually fine












Yeah, that’s going beyond the software and making the physical supply chain possible to validate by a sufficiently equipped and educated consumer
The trade off here is that it’s very difficult to produce verifiable circuitry that is also fast